Blog
-
Perfecting Productivity, Part Three: Protecting Productivity
We’ve been spending the past few weeks examining productivity and how to optimize it, and today, we felt it was necessary to address the issues that could throw the proverbial wrench into the works. Don’t worry, though, we’re also going to touch on how you can avoid and/or mitigate the issues that might threaten your…
-
Just Because Google Chrome Offers Password Management Doesn’t Mean You Should Use It
One of the reasons that information technology keeps changing is for the sake of the user and their convenience using it. However, if this convenience comes at the sacrifice of your business’ cybersecurity, it just isn’t worth it.
-
Does Your Data Backup Comply with the 3-2-1 Rule
Today, we want to take a closer look at the 3-2-1 rule and how it impacts your business’ ability to recover in the face of a disaster. Let’s dive in and see how the 3-2-1 rule can make or break your company’s data infrastructure.
-
Tip of the Week: 3 Steps to Avoiding a Ransomware Infection
Ransomware is a huge threat that today’s businesses need to be prepared to deal with. In light of this, we wanted to share a few tips to help you avoid the negative ramifications of ransomware.
-
The Biggest Risk Is Not The One You Don’t Take, But The One You Don’t See
If you follow Warren Buffett’s two rules of investing, you’ll see this same caution: Rule #1 – Never lose money. Rule #2 – Never forget Rule #1.
-
Why Solid Project Management is So Important
Cyberattacks are a serious problem that all businesses face in some form or another, but there are small, everyday tasks you can do to ensure that they impact your organization as minimally as possible.
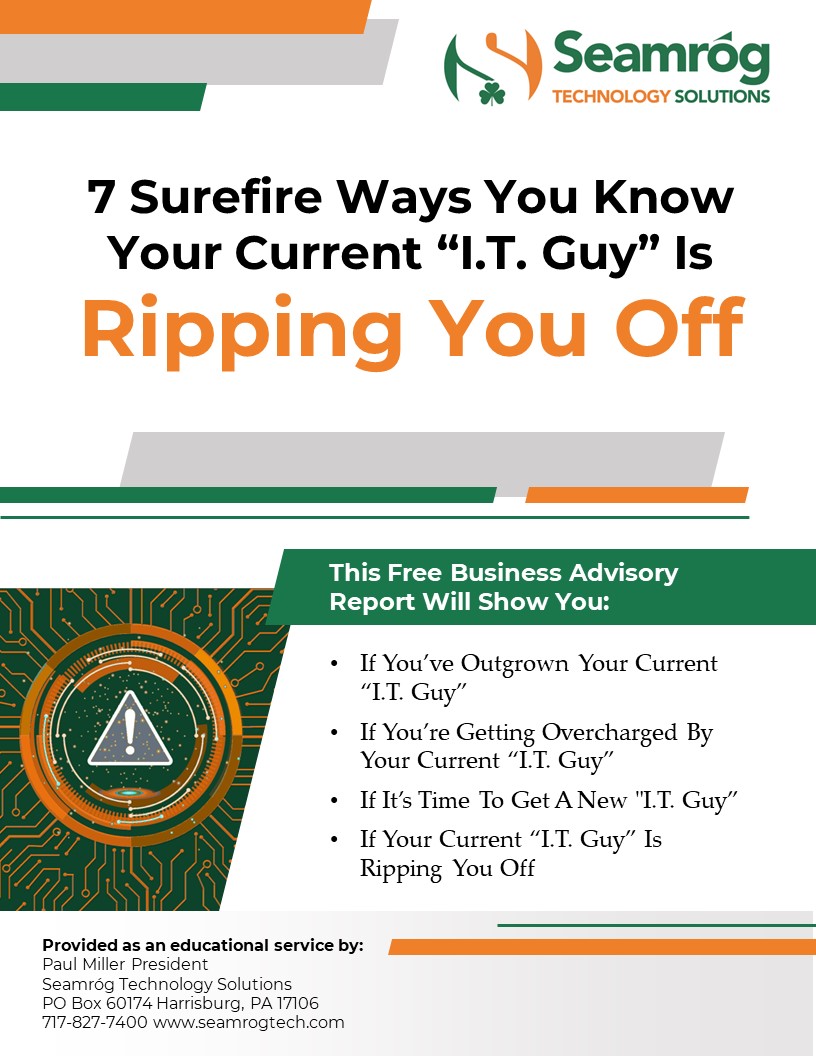
Free Download!
7 Surefire Ways Your Current ‘I.T. Guy’ Is Ripping You Off






