Tip of the Week: How to Keep MFA Fatigue from Being a Security Vulnerability
One method hackers use to gain access to your systems is to use what’s called MFA fatigue to their
Read More
One method hackers use to gain access to your systems is to use what’s called MFA fatigue to their
Read More
It’s okay to feel overwhelmed and to not know enough about certain things in business... we can help
Read More
Many businesses, seeking to balance the positives brought by remote work to the value that in-person, face-to-face operations have to offer, have leaned into
Read More
Let’s talk about what really happens when you’re doing so—chances are, you may be overlooking a serious security
Read More
Unfortunately, ransomware attack comes with a lot more financial impact than just the payment the attacker
Read More
There is always the possibility that you have been involved with a data breach and you simply have not been contacted by the affected
Read More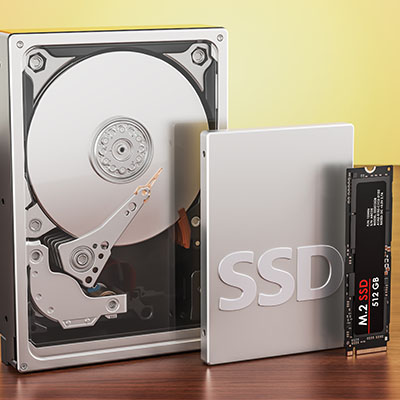
What’s the difference between your typical hard drive and an SSD, you ask? Well, today we’ll find
Read More
Hackers are always looking for new ways to infect
Read More
Every business depends on productivity, but there are many different forms that productivity can take.
Read More
Let’s take a look at what makes up the Internet of Things and why it’s important to know what it is from a business
Read More